Technology
Innovation of Computers Which Changed the World & The World of Cyber Threats
As of now, the corporate sector is experiencing the advantages of computer reduction and greater mobility.
As computers, netbooks, PDAs, and smartphones have grown more and more commonplace, it has become easier to work while on the go, blurring the barrier between work and home life.
Trends in computers, we do our best to look forward one year at a time and identify the major technological developments that will have a significant impact over the next months.
If we are talking about the revolution, it’s like a moment in time at which computers bring about substantial changes to human civilization is referred to as a computer revolution.
There has been a shift from mechanical and analog electrical technologies to electronic ones, beginning in the late twentieth century, as computers and digital record-keeping became more widely accepted today.
Table of Contents
Evolution of Technology
· First PC And Digitilization
In 1972, the microprocessor was created, and the power of computers soared while their size decreased significantly.
With computing on a little chip, personal computers might be accessible to the public. This was the first time that personal computers could be offered to the general public as a product.
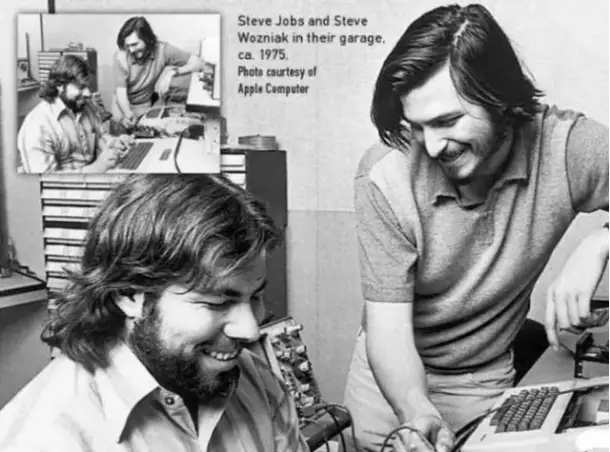
IBM produced the IBM PC in 1981, and Steve Jobs followed up with Apple Computer and its “Macintosh” series. (Wegberg, M. (n.d.). Evolution and Competition in the Market for Handheld Computers. Core.Com. Retrieved August 22, 2019)
· Microsoft and Apple War: The Change of Revolution In the Computer Industry
In the 1980s and 1990s, computer innovation concentrated on hardware and software. Because of Windows, computers became more widely available to the general public and enterprises. To make things like logos, product designs, word processing, report compilation, and the increasingly complicated computations required by the high-tech sector, computers were frequently being utilized by this point.
The Apple and Microsoft war in the Market Started back in the 90s when apple followed the UNIX Gui and Program it to develop their Operating System; Apple’s rapid growth and collapse. Newton is a fascinating example of how the mobile industry has evolved.
According to a Moscow report, handwriting recognition is Newton’s defining feature. In contrast, Apple licensed the Newton system on their Macintosh operating system. When it was first released, the Newton cost a hefty $699. The only way to enter data was using a mouse. The lack of a keyboard has the benefit of reducing the overall size of the Newton, though. The Newton technique was not part of Apple’s long-term strategy.
Apple raised many hopes for the Newton before it was even released. Apple is also a concern as it has a minimal relationship with the industrial computer industry.
Sharp has lent its support, but Microsoft has the backing of many industry giants. Because of Apple’s difficulties developing and promoting the Newton, competitors were given an opening. In 1996, HP introduced the Graffiti handwriting recognition software together with the GEOS operating system. It is clear from the PalmPilot’s popularity that Apple’s product lacked coherence: restricted options at a premium price.
Pen-based computers made by Microsoft, on the other hand, were the first to arrive on the market. Developing a portable computer around its software was the only economically viable option for Palm Computer. As a result of the Pilot’s popularity, many competitors have emerged. At least two attempts were made by Microsoft to fit the 16-bit Windows 3.1 operating system into a tiny space.
Modular Windows, an operating system for interactive television, and Win pad, an operating system for portable devices, were both created by it by 1992. To further extend its dominance in PCs onto handhelds, it created Microsoft Windows for Pen Computing. Intel CPUs and their corresponding memory requirements.
Windows exceeds the limitations of a portable computer. Operating systems for portable computers based on Windows 95 or Windows NT. Three operating systems have been replaced by Microsoft’s Windows CE approach.
The Psion Series 3a handheld was released in 1993, five years before introducing the Windows CE 2.0 portable. (Wegberg, M. (n.d.). Evolution and Competition in the Market for Handheld Computers. Core.Com. Retrieved August 22, 2019)
Business, Computers & Internet
The widespread usage of the Internet in the late 1990s led to an explosion of efficiency improvements, including the capacity to coordinate design, manufacture, distribution, and sales via computer systems and the networks that linked them. As a result of real-time global commerce, national governments’ influence was reduced.
As bandwidths increased, teleconferencing and telecommuting became inexpensive and effective, enabling outsourcing and other 21st-century commercial practices.
Problem Statement
As the world is moving towards advanced technologies in 21st century, The protection of sensitive information is one of the primary concerns of any government, particularly given the increasing prevalence of digital formats and cyberspace for the storage and transmission of data throughout the globe.
Cybersecurity is essential for today’s businesses as the world is growing in the technology sector and expanding. Theft of proprietary data, identity theft, and other cybercrimes are rampant, costing organizations millions of dollars each year.
People should be able to feel comfortable while connecting with other users anywhere around the globe, which is made possible by many of the social media platforms available today and security solutions.
The illegal activities discussed here have as their primary objective social media platforms to access confidential information and target different organizations. In addition to using social media, users looked for advice on how to exercise the necessary level of care while doing other kinds of transactions online, such as banking transactions.
References: europarl.europa.eu
Problems Faced in Cybersecurity
In general, there are two different sorts of risks associated with cybersecurity. The first of these risks is known as actioned means, for they are suggested to create bad effects on digital media systems. The second type of risk is known as some course of action, which is a necessity for exploiting the infrastructure of cyber or some harmful purposes without having any kind of damage which may have the repercussions at once result on the functioning of a system like there was a Trojan Horse, and it is beneficial for making negative impacts.
The purpose of passing on uncertain messages that link political and detest discourse, supplying suggestive excitement to minors, and having an infringement of copyrights are all examples of ways that the Internet and other forms of digital media may be used inappropriately. Other ways that the Internet can be misused include using it to submit any extortion like taking, planning mental oppressor, and having an entrance of copyrights.
Objective of Research
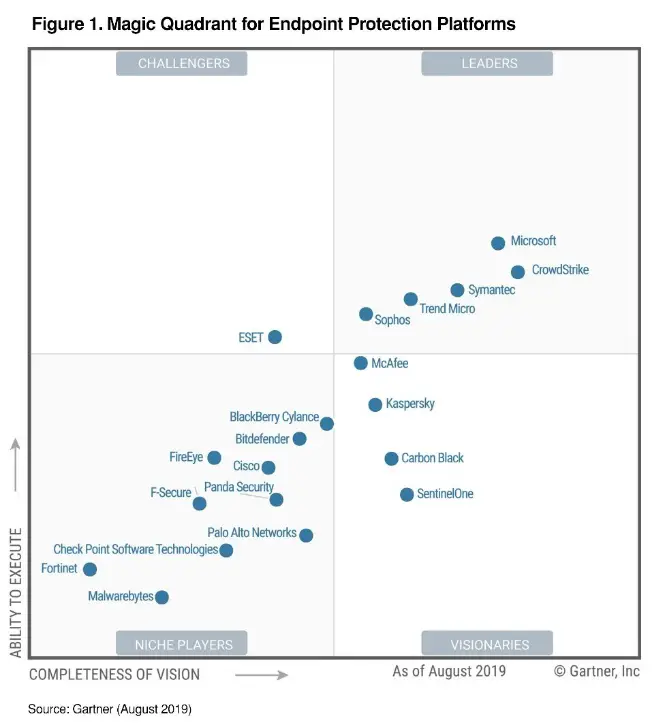
Endpoint Solutions Security AI-Based Applications
To automate the threats, programming devices are being used. With this product and preconfigured cyberattacks, a single guilty person may attack several PC frameworks in a single day by using a single PC. If the guilty person can access at least one computer.
Not all assaults are successful since most products are readily accessible, but the method for cyberattacks is effective. The AI-Based Software Solutions like Endpoint Security offered by several companies like Microsoft, Fire eye, Kaspersky, and some others which helps organizations gets secured and Most Advanced Version Self Learning AI Based Technology.
When clients update their systems and applications often, they reduce the risk of becoming victims of these large-scale assaults since the business also does security software inspections and plans for them in advance.
Question Research
- In what ways will cyber security evolve over time?
- What are some of the biggest hurdles to adopting cybersecurity?
- In 2022, what are the most serious cybersecurity threats?
- What are the most essential features of cyber security?
- Exactly what kinds of companies are most vulnerable to a cyberattack?
- What are the Future of Upcoming Computers?
Methodology:
In recent years, businesses have become increasingly reliant on technology. From online banking and shopping to using cloud-based storage, businesses rely on technology for almost everything. This makes businesses a prime target for cyberattacks.
A cyberattack can cause significant financial damage, jeopardize the safety of employees and customers, and damage a company’s reputation. The most serious cybersecurity threats are Phishing Attacks, Malware Attacks, Ransomware, Weak Passwords, and Insider Threats, and There are a lot of methods that is invented.
Despite the risks, many businesses do not take the necessary precautions to protect themselves from cyberattacks.
One reason for this is that many business owners underestimate the risk of a cyberattack or do not understand the magnitude of the damage that can be caused.
Another reason is that businesses often do not have the budget to invest in cybersecurity measures.
However, it is important for businesses to realize that cybersecurity is not an option but rather a necessity in today’s world.
Microsoft and other companies have developed advanced AI Based Security Solutions for Corporations and Organizations in order to protect:
It is the goal to introduce additional design phase efforts for new cyber physical systems with a fast and efficient procedure that satisfies the system’s cyber security needs.
When designing a new system, the various components of cyber security (e.g., cyber-attack protection, cyber-attack resilience) should be combined in order to get the optimum results. Important early choices about system architecture may be made at this phase of the system design process. Some examples of these initial decisions include the following:
- The separation and isolation of hardware and software that supports distinct system functions;
- History of cyber assaults must be considered while purchasing off-the-shelf items.
- With particular solutions to be picked after the concept is mature, reliance on defensive capabilities
- When developing a new system, how much attention and resources should be placed on the software development process? (Quality assurance tools, testing, developer skills, life cycle support, etc.),
- Specification requirements for resilience-related capabilities, both present and future, in order to make it easier to add more capabilities in the future.
- Taking into account the characteristics of resilience that are connected to the operator via the use of fast prototyping trials and exercise-related support tools.
Data Analysis:
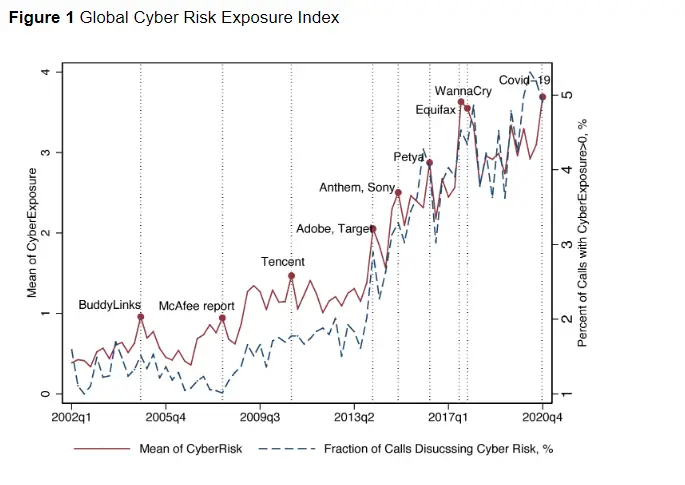
Reference: voxeu.org
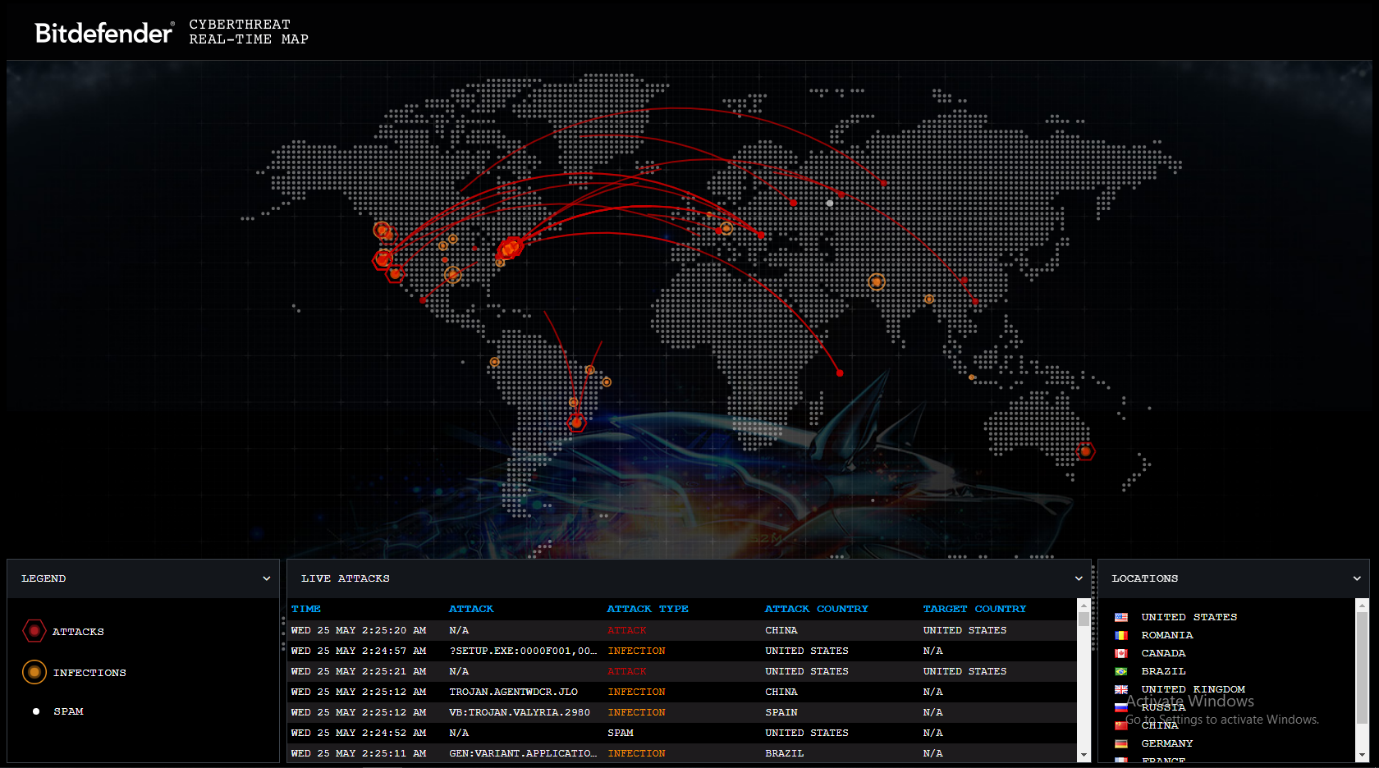
Reference: Bitdefender
Cyber Attacks Worldwide Graph
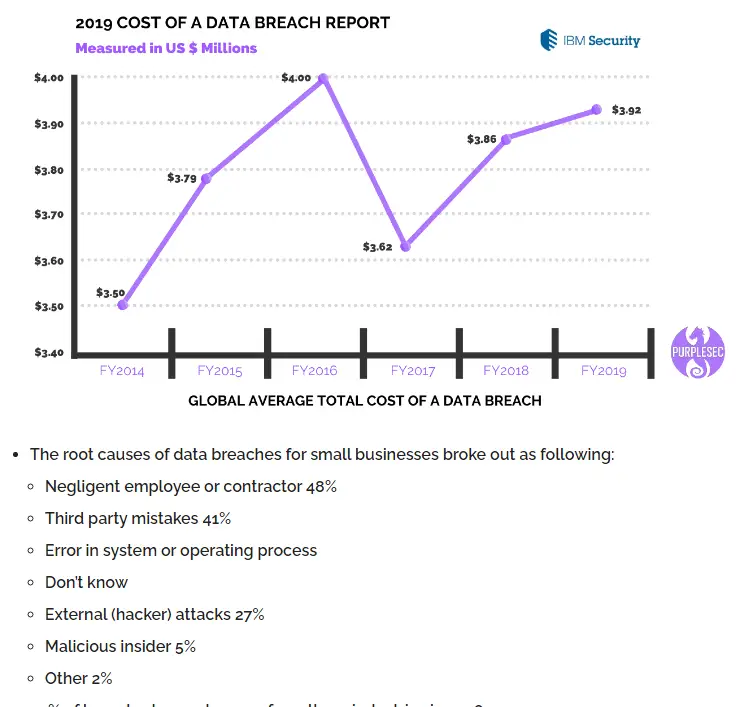
Reference: IBM Security
Conclusion
Because of the increasing global connectivity, the issue of cybersecurity has become more important.
More and more important transactions are being carried out on personal computer systems. Companies are being forced to consider the safety of their computer systems because of the proliferation of innovative technologies, the development of more advanced digital security tools, and the daily discovery of new digital threats.
As a result, these companies require advanced platforms and tools to secure their computer systems.
There is currently no conclusive response available to digital assaults. In any event, we need to do all in our power to reduce the amount of cybercrime.
References
- https://core.ac.uk/download/pdf/6908827.pdf
- https://www.europarl.europa.eu/news/en/headlines/society/20220120STO21428/cybersecurity-main-and-emerging-threats-in-2021-infographic
- https://www.microsoft.com/en-ww/security/business/microsoft-endpoint-manager
- https://www.cio.com/article/242299/history-of-apple-and-microsoft-4-decades-of-peaks-and-valleys.html
- https://www.kaspersky.com/small-to-medium-business-security
- https://dl.acm.org/doi/abs/10.1145/3327960.3332393
- https://apps.dtic.mil/sti/pdfs/AD1057439.pdf
- https://voxeu.org/article/anatomy-cyber-risk
Research and Term Paper By Ali Ahmed (Author) – NU

A blog which focuses on business, Networth, Technology, Entrepreneurship, Self Improvement, Celebrities, Top Lists, Travelling, Health, and lifestyle. A source that provides you with each and every top piece of information about the world. We cover various different topics.
Technology
With ‘F1’, Apple finally has a theatrical hit

Looks like Apple has its first bona fide box office hit.
The company has already produced critically-acclaimed and award-winning films for Apple TV+. In fact, while Netflix has reportedly spent millions on its Oscar campaigns, Apple’s “Coda” remains the only movie produced by a streaming service to win the Academy Award for Best Picture.
It has, however, been a different story at the box office — at best, returns have fallen short of ambitious budgets, and with “Argylle,” the company had a spectacular flop. Last year, Apple reportedly decided to scale back on both budgets and theatrical releases, leading to canceled projects and criticism from directors.
Things have finally turned around with “F1” — currently the number one movie in theaters, on-track to earn $55.6 million this weekend at the domestic box office. With $144 million in global ticket sales, “F1” will soon surpass “Napoleon” ($228 million) as Apple’s highest-grossing film.
“F1”’s director, Joseph Kosinski, previously helmed “Top Gun: Maverick,” and in many ways, the new movie sounds like a loose copy of the “Maverick” formula, combining realistic, you-are-there cinematography (Brad Pitt is really driving those cars!) with a familiar narrative about an older veteran forced to work with a young upstart who needs to learn a thing or two about old-fashioned, analog grit.
“F1” (which is being distributed in the U.S. by Warner Bros.) likely benefited from the surging U.S. popularity of Formula One racing, fueled in part by Netflix’s docuseries “Drive to Survive.” Much of it was filmed at actual Formula One races, and driver Lewis Hamilton also signed on as a producer.
Apple CEO Tim Cook even joined Hamilton for a Variety cover story in which Cook said the company was able to “bring some things that were uniquely Apple to the movie, like our camera technology.” The plan, he added, was “to have the whole of the company support it as well — our retail operation and everything.” (Not all customers have been pleased with the cross-promotion.)
While Apple’s bet seems to be paying off, it’s still not clear whether “F1” — with a reported budget of more than $200 million — will actually make a profit in theaters. Before its release, one box office analyst told Vulture that even in success, the movie “may end up being a very expensive commercial for original content on Apple TV.”

A blog which focuses on business, Networth, Technology, Entrepreneurship, Self Improvement, Celebrities, Top Lists, Travelling, Health, and lifestyle. A source that provides you with each and every top piece of information about the world. We cover various different topics.
Technology
Trump says he’s found a buyer for TikTok

A group of “very wealthy people” is set to buy short-form video app TikTok, according to President Donald Trump.
“We have a buyer for TikTok, by the way,” Trump said in a Fox News interview on Sunday morning. “I think I’ll need probably China’s approval. I think President Xi [Jinping] will probably do it.”
Trump declined to share more details about the buyers, saying only that he would reveal their identities in two weeks (apparently his favorite unit of time).
Trump has repeatedly delayed a bill forcing owner ByteDance to sell the app or see it banned in the United States. In January, he said his “initial thought” was to create “a joint venture between the current owners and/or new owners whereby the U.S. gets a 50% ownership.”
He’s also said he was open to allies Larry Ellison or Elon Musk buying the app, although Musk seems like a less likely candidate now.

A blog which focuses on business, Networth, Technology, Entrepreneurship, Self Improvement, Celebrities, Top Lists, Travelling, Health, and lifestyle. A source that provides you with each and every top piece of information about the world. We cover various different topics.
Technology
Meta reportedly hires four more researchers from OpenAI
Looks like Meta isn’t done poaching talent from OpenAI.
Earlier this week, TechCrunch reported that Meta had hired influential OpenAI researcher Trapit Bansal, and according to The Wall Street Journal, it also hired three other researchers from the company.
Now The Information is reporting four more Meta hires from OpenAI: Researchers Shengjia Zhao, Jiahui Yu, Shuchao Bi, and Hongyu Ren.
This hiring spree comes after the April launch of Meta’s Llama 4 AI models, which reportedly did not perform as well as CEO Mark Zuckerberg had hoped. (The company was also criticized over the version of Llama that it used for a popular benchmark.)
There’s been some back-and-forth between the two companies, with OpenAI CEO Sam Altman suggesting that Meta was offering “$100 million signing bonuses” while adding that “so far, none of our best people” have left. Meta CTO Andrew Bosworth then told employees that while senior leaders may have been offered that kind of money, “the actual terms of the offer” were more complex than a simple one-time signing bonus.

A blog which focuses on business, Networth, Technology, Entrepreneurship, Self Improvement, Celebrities, Top Lists, Travelling, Health, and lifestyle. A source that provides you with each and every top piece of information about the world. We cover various different topics.
-

 Technology3 weeks ago
Technology3 weeks agoMeta AI gains video editing capabilities
-

 Travel3 weeks ago
Travel3 weeks agoBook Ban Spread: Michigan Schools Join a Growing National Trend
-

 Life Style2 weeks ago
Life Style2 weeks ago6 Summer Tips for Unwinding, Recharging and Taking Care of Yourself
-

 Life Style3 weeks ago
Life Style3 weeks agoThe Top 10 Ways to Be Kind to Yourself Starting Today
-
News2 weeks ago
A Timeline of the Minnesota Shooting
-

 Travel3 weeks ago
Travel3 weeks ago9 Funny New York Town Names That’ll Make You Do a Double Take
-

 Technology3 weeks ago
Technology3 weeks agoThe Meta AI app is a privacy disaster
-

 Technology3 weeks ago
Technology3 weeks agoVijay Pande, founding partner of a16z bio and health strategy, steps down