Technology
7 Best Ways To Protect Yourself Against Hackers

The internet has revolutionized the way we do business and communicate, but to an extent it seems that this great technology may also pose some risks. According to McAfee’s 2011 Threats Report, instances of hacking are on the rise. The report reports “an 866 percent increase in malware over last year, with credit card stealing Trojans up an awesome 3,566 percent.”
Hackers are a frightening bunch whether or not working as a part of a criminal syndicate or an idealist with a political timetable, they were given the information and the energy to access your important record. Down below are the 7 best Ways To Protect Against Hackers.
This article’s aim is to focus on some most common ways that hackers access your information and give you a brief overview of how to defend yourself from their tactics.
Think of your home laptop or PC as a company. What are you able to do to shield it towards hackers? Or opposed to sitting again and ready to get inflamed, why no longer arm yourself and combat again?
Table of Contents
Here are 7 best ways to protect against hackers:
1. Keep Your Software Up-to-date
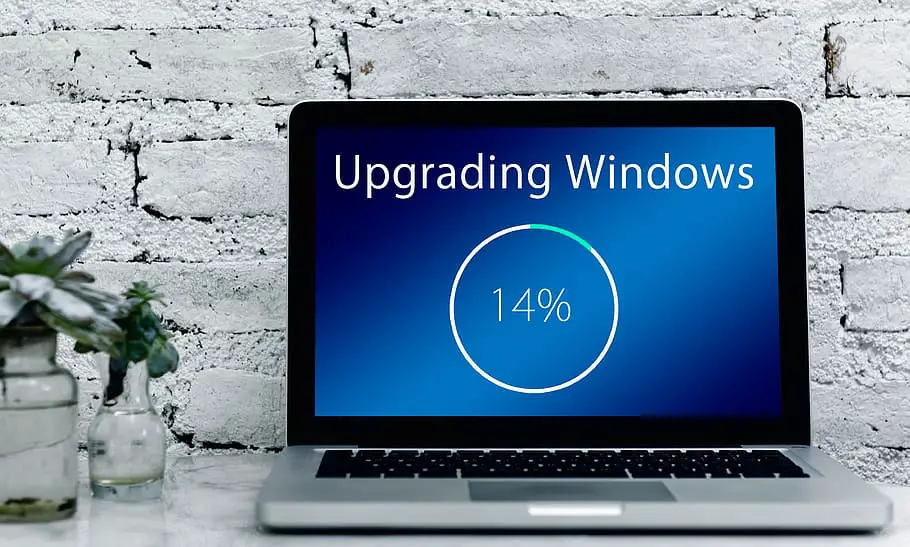
Keep updating your Operating System and other software programs regularly. This keeps hackers from accessing your laptop via vulnerabilities in old packages.
For additional protection, enable Microsoft product updates in order that the Office suite may be updated on the regular basis. Keep in mind retiring especially old software program including java or flash.
According to a survey by Microsoft Corp., security breaches fell by 40% in 2010 as a result of criminals targeting older versions of software with known security flaws.
To protect yourself, always update your operating system and web browser to the latest version. Also, enable Auto-updates on all your other applications that have them available.
2. Download Updated Antivirus Software’s:

Keep up to date protection programs, together with antivirus and anti-malware software program, anti-spyware, and a firewall. To trick even the maximum villainous hackers, don’t forget investing in anti-exploit technology, such as Malwarebytes anti-exploit so that you can prevent attacks earlier than they show up.
Make sure that you are downloading antivirus software from legitimate software providers.
There are many websites that offer free downloads of antimalware program, but they are not the official website.
Be very careful when installing them because many of them come with spyware or malware programs.
While most antivirus software has their own updates, it is still important that you download the latest updates to fix security holes.
You can do this by checking the antivirus software’s website for updates or you can set your computer to automatically update it.
10 Simple Steps to Boost Your Wi-Fi Speed
3. Do not Use Open Wifi:

Hackers use open Wi-Fi connections to gain access to user’s personal information. Protect your wifi with an encrypted password, and remember fresh your device every few years.
Some routers have vulnerabilities which can be never patched. Newer routers let you provide guests with segregated wireless access. They make common password changes very easy.
This is very easy for people that are using mobile phones or laptops because most wireless networks are unprotected for anyone to use. There are several ways that hackers can gain access to your personal information by using open wifi.
One way is to put up a fake wifi connection that looks very real. When someone tries to connect, the hackers can capture all of their personal information. This is known as a man in the middle attack.
Another way is through IP spoofing. This is when the hacker changes their IP address to match yours so they can get access to your internet.
All they have to do is enter the same IP address, subnet mask and default gateway as yours. The last way that they can gain access is by using packet sniffing. This happens when a hacker watches all traffic being sent from you or to you without being detected.
4. Use Complex Password to Protect Your Devices:

People can hack into your accounts if you use very easy passwords to access them. They might use a dictionary or they might try and figure out your password with trial and error. An easy way to make sure that your information stays secure is by using complex passwords.
This will make it harder for hackers to access your information. You should also try to change your password regularly so that it is always secure. People can access old passwords very easily if you haven’t changed them for a long period of time.
The ubiquity of mobile devices makes them mainly vulnerable. Lock your phone and make the timeout pretty short.
Use fingerprint lock for the iPhone and passkey or swipe for Android. This makes difficult for hackers to access your devices.
5. Remove Unknown Emails:
In case you receive e-mails from a random person, do no longer hassle to open the email, simply delete it. If you have any doubts after reading the call and the situation, it’s probably not a person you recognize. Never download or open attachments unless you are positive it’s from someone.
People are most likely to become hacked by opening the wrong email. This is because most people don’t even bother checking their emails anymore. You should always check your emails before you download something or click on a link inside it.
If you have an email that doesn’t have any writing or pictures in it, this means that it is spam. You should delete these emails because there might be a virus or some kind of malware attached to them.
You should also watch out for fake emails from companies that you do business with. These fake emails will have similar names as the company’s CEO and they will ask you to disclose personal information such as your password.
This is a trick to get your information so that they can hack into your account.
New App that Reveals ‘Wifi Passwords’ of Airports around the world
6. Keep Sensitive Data Off the Clouds:

Many people use services like Dropbox or Google Drive to keep copies of their files in the cloud, but even if you encrypt your sensitive data with a long password before uploading it, there is still a good chance hackers will be able to gain access. It’s not because these services are insecure.
They may have very high levels of security — but because they are a type of cloud service that allows you to share files with others. So, if your password is compromised and someone else uploads a virus or spyware to your account, suddenly your sensitive data is easily accessible by hackers.
Keep sensitive data off the cloud. No matter which way you cut it, data stored in the cloud doesn’t belong to you. There are very few cloud storage solutions that offer encryption for ‘data at rest.’ Use the cloud accordingly. If it’s important, don’t.
10 New Awesome Technologies That Will Change Our World in Future
7. Avoid Clicking Ads:
Most of us are used to clicking on ads but have you ever stopped to think about where these ads are taking you?
If the ad contains a link, it is most likely going to be an affiliate website. These websites will try and get you to sign up for different things so they can earn money from your clicks.
You have to surf the internet smartly. Avoid clicking on ads if you can. Especially the one’s ads where something is flying around and if you shoot the duck, you win a few prize! advertisements have come to be more sophisticated in that they are trying to make the advert interactive so you’ll be tempted to play it like a game.
Conclusion
As the world becomes more and more connected, hackers are going to find new ways of making money. However, you can protect your data by following a few simple steps outlined here in this blog post.
What else do you think is important for protecting your digital life? Let us know what we missed!

A blog which focuses on business, Networth, Technology, Entrepreneurship, Self Improvement, Celebrities, Top Lists, Travelling, Health, and lifestyle. A source that provides you with each and every top piece of information about the world. We cover various different topics.
Technology
Trump says he’s found a buyer for TikTok

A group of “very wealthy people” is set to buy short-form video app TikTok, according to President Donald Trump.
“We have a buyer for TikTok, by the way,” Trump said in a Fox News interview on Sunday morning. “I think I’ll need probably China’s approval. I think President Xi [Jinping] will probably do it.”
Trump declined to share more details about the buyers, saying only that he would reveal their identities in two weeks (apparently his favorite unit of time).
Trump has repeatedly delayed a bill forcing owner ByteDance to sell the app or see it banned in the United States. In January, he said his “initial thought” was to create “a joint venture between the current owners and/or new owners whereby the U.S. gets a 50% ownership.”
He’s also said he was open to allies Larry Ellison or Elon Musk buying the app, although Musk seems like a less likely candidate now.

A blog which focuses on business, Networth, Technology, Entrepreneurship, Self Improvement, Celebrities, Top Lists, Travelling, Health, and lifestyle. A source that provides you with each and every top piece of information about the world. We cover various different topics.
Technology
Meta reportedly hires four more researchers from OpenAI
Looks like Meta isn’t done poaching talent from OpenAI.
Earlier this week, TechCrunch reported that Meta had hired influential OpenAI researcher Trapit Bansal, and according to The Wall Street Journal, it also hired three other researchers from the company.
Now The Information is reporting four more Meta hires from OpenAI: Researchers Shengjia Zhao, Jiahui Yu, Shuchao Bi, and Hongyu Ren.
This hiring spree comes after the April launch of Meta’s Llama 4 AI models, which reportedly did not perform as well as CEO Mark Zuckerberg had hoped. (The company was also criticized over the version of Llama that it used for a popular benchmark.)
There’s been some back-and-forth between the two companies, with OpenAI CEO Sam Altman suggesting that Meta was offering “$100 million signing bonuses” while adding that “so far, none of our best people” have left. Meta CTO Andrew Bosworth then told employees that while senior leaders may have been offered that kind of money, “the actual terms of the offer” were more complex than a simple one-time signing bonus.

A blog which focuses on business, Networth, Technology, Entrepreneurship, Self Improvement, Celebrities, Top Lists, Travelling, Health, and lifestyle. A source that provides you with each and every top piece of information about the world. We cover various different topics.
Technology
YouTube’s mobile video editor is coming to iOS
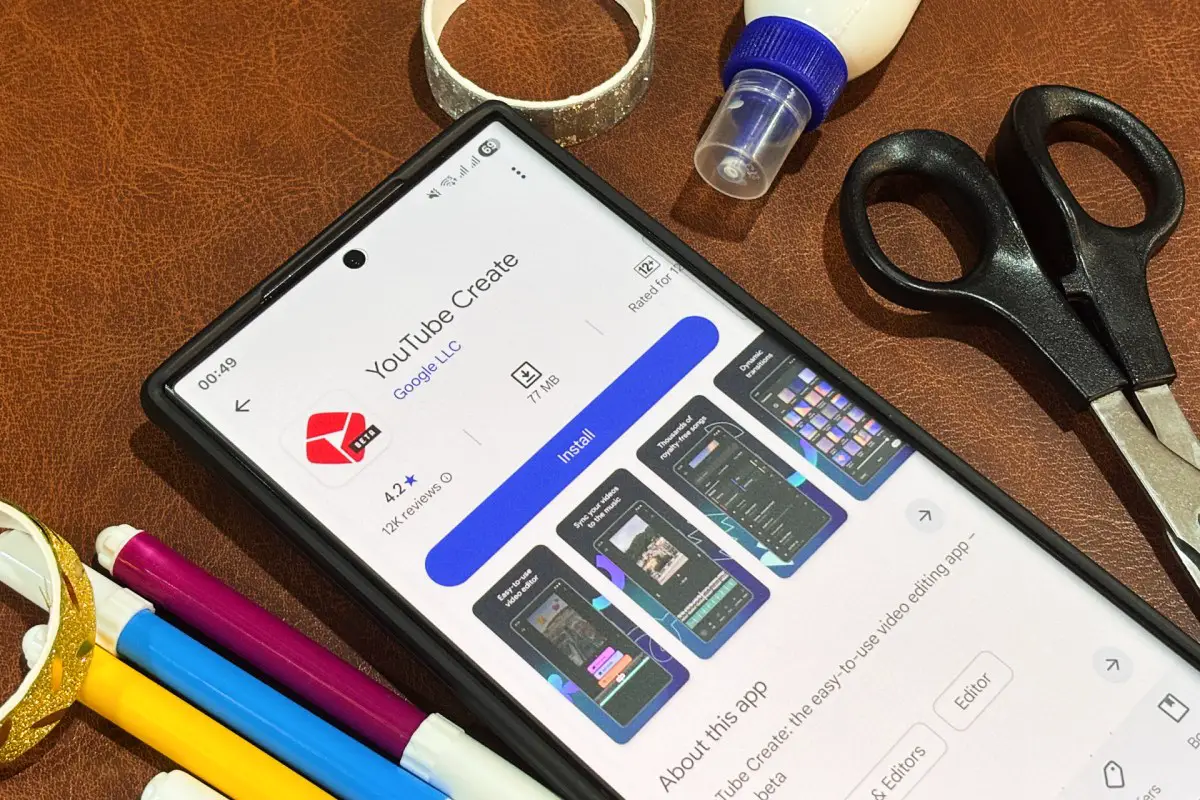
Google is preparing to bring YouTube Create to iOS devices nearly two years after the video editing app launched exclusively on Android. Job listings reviewed by TechCrunch reveal the company is actively hiring engineers in India for the iOS development project.
The job postings show Google is recruiting software engineers in Bengaluru specifically to build the iOS version. The original Android app debuted in the U.S. and seven other markets in September 2023, then expanded to 13 more markets by February 2024.
YouTube Create provides free mobile video editing tools designed for content creators, offering features like stickers, GIFs, and effects for both YouTube Shorts and longer-form videos. Google developed the app after consulting with 3,000 creators to ensure it met their needs.
The app is Google’s attempt to compete with ByteDance’s popular CapCut editor. But exclusive Sensor Tower data shared with TechCrunch shows YouTube Create is quite far behind CapCut and another established competitor, InShot.
The competition isn’t even close. In the second quarter of this year, CapCut and InShot have been downloaded 66 million and 21 million times, respectively, on Android devices. In contrast, YouTube Create has seen fewer than 500,000 downloads this quarter and just 4 million downloads since its launch.
The user engagement gap is even more pronounced. CapCut boasts more than 442 million monthly active users on the Android app in Q2, while InShot claims 92 million. YouTube Create lags far behind with fewer than 1 million monthly active users.

On iOS — the platform YouTube Create is now targeting — the competition is just as fierce. CapCut leads with 194 million monthly active users in Q2, followed by InShot with 25 million. Meanwhile, CapCut and Instagram’s Edit have dominated iOS downloads this quarter, with 28 million and 7 million downloads, respectively.
Despite lagging in the numbers, YouTube Create shows some momentum, with a 28% year-over-year increase in monthly active users in Q2, outpacing a 9% rise for CapCut and a 7% decline for InShot, per the Sensor Tower data.
“While boasting solid user growth on a year-over-year basis, YouTube Create has struggled to keep up with some of its larger, more established peers such as CapCut, with the latter having more than 10x the number of monthly active users,” said Abe Yousef, a senior insights analyst at Sensor Tower.
YouTube Create may be building a more loyal user base, Yousef suggested. Rising active user numbers alongside declining downloads could indicate that people who previously tried the app are returning to use it regularly.
“CapCut coming out many years ago, coupled with the fact that it’s seamlessly integrated with its sister app, TikTok, likely plays into this material size difference with YouTube Create,” said Yousef.
Still, YouTube Create is facing some retention issues. Its 90-day retention rate — the percentage of users who downloaded the app and still use it 90 days later — was roughly 1% in Q1, far below CapCut’s 7% and InShot’s 4%.
Engagement metrics highlight the gap, too. Users spend an average of 38 minutes per month on YouTube Create, compared to 62 minutes for CapCut users. CapCut users also open the app more often, averaging 23 sessions monthly versus 11 for YouTube Create.
Geographically, YouTube Create’s user base is diversifying. India represented 67% of total monthly active users on YouTube Create in the second quarter of last year, but that share has dropped to 51% this quarter as the app gains traction elsewhere. Still, YouTube Create appears to be gaining stickiness in India, with daily-to-monthly active user ratios improving from 9% last year to, so far, 12% this year.
In addition to India, Indonesia has emerged as YouTube Create’s second-largest market, representing 21% of its global monthly active users. Germany (5%), Brazil (4%), and the U.K. (3%) round out the top markets.
The app is showing particularly strong growth in several other markets, too, with year-over-year monthly active user increases of 119% in Spain, 91% in South Korea, 89% in France, and 71% in Singapore.
“An iOS release of YouTube Create could absolutely help the platform grow its market share, though fierce competition in the space both from other social media-backed video editing platforms and native video editors will persist,” Yousef said.
Google did not respond to requests for comment.

A blog which focuses on business, Networth, Technology, Entrepreneurship, Self Improvement, Celebrities, Top Lists, Travelling, Health, and lifestyle. A source that provides you with each and every top piece of information about the world. We cover various different topics.
-

 Life Style3 weeks ago
Life Style3 weeks agoPositive and Funny Sayings for Students, Parents and Teachers
-

 Technology3 weeks ago
Technology3 weeks agoMeta AI gains video editing capabilities
-

 Travel3 weeks ago
Travel3 weeks agoBook Ban Spread: Michigan Schools Join a Growing National Trend
-

 Travel3 weeks ago
Travel3 weeks agoSouth Carolina Ranks High for Military Retiree Care—Where Does Your State Stand?
-

 Life Style2 weeks ago
Life Style2 weeks ago6 Summer Tips for Unwinding, Recharging and Taking Care of Yourself
-

 Life Style2 weeks ago
Life Style2 weeks agoThe Top 10 Ways to Be Kind to Yourself Starting Today
-
News2 weeks ago
A Timeline of the Minnesota Shooting
-

 Travel2 weeks ago
Travel2 weeks ago9 Funny New York Town Names That’ll Make You Do a Double Take