Technology
2 Modems In One Home: How It Works (Explained)

Setting up two separate lines of communication for your computer can seem like a daunting task at times! There are several ways to do this, but one of the most popular is using a router as both your modem and wifi access point.
A router acts as the brain that connects all of your devices together- you connect peripherals (laptops, phones, gaming consoles, etc.) to it via USB or Ethernet cables, and then it routes those signals either directly to another device or through its internet service provider (ISP).
A lot of people use routers this way because they’re built with powerful software that makes connecting easy. Some features even allow for multitasking by letting you use the browser while still being connected online!
There are many brands of routers, so pick one that fits your needs and budget well. However, make sure it has enough bandwidth for all of your uses and fun! We could not finish this article listening to the sounds of some poor connections.
Editorial note: For more information about why having multiple sources of Internet connectivity is important, check out our article here.
This article will go into detail on how to install and use a dual-band modem/router in conjunction with WiFi. It will also talk about the benefits of using a dual-mode connection, and where things may get tricky.
What is a router?
A device that connects to your internet provider’s network is called a router. Most people call them that, but what most don’t know is that there are different types of routers!
There are two main types of routers — those for work and those for personal use. Work-level routers usually have more features than personal ones, but you will need a good quality one if you plan to connect multiple devices to yours at home.
Work-level routers typically cost around $100 – $150, while personal level ones can be much less expensive. It really depends on how many connections you want to make and what kind of speeds you desire.
How do they differ?

Like having two separate phones, one wireless connection can be tough at times. With dual-mode (or modem) technology, your phone doesn’t connect directly with other devices or computers via WiFi or Bluetooth, but rather uses a second device as a backhaul router.
This way, it has its own dedicated broadband connection that helps ensure fast internet for use and sharing.
You get all of the benefits of having a normal modem connected to a house wifi network, without the cost – and headaches – of adding another device you have to take care of.
Can You Have 2 Modems In One House?
Having more than one modem is possible, but only if you live in a very specific situation! This article will talk about all of the scenarios where this can be done, as well as what to consider before purchasing one or two modems.
It’s important to remember that even though it seems like a great idea, not everyone has the same internet connection speed. Some people are lucky enough to have a fast home wifi network, while others do not.
For those individuals who don’t have good wifi at home, there are sometimes services that offer fiber optic broadband so that they can connect via cable instead.
This is much faster than using wifi and cable TV bundles which usually limit how many online apps you can use because of bandwidth constraints. It is totally up to you whether or not this information changes your opinion on whether or not you need a second modem.
What are the advantages?
Setting up two separate lines of communication with different providers can be done several ways. Some people connect one modem directly to each provider, while others use a router as an intermediary. Both work fine!
In this article we will discuss what is called “split service” or “dual-band technology,” which allows you to have both Verizon and AT&T phone services through the same device. This is possible because most wireless carriers offer their own LTE (4G) network that does not require a data connection to function.
You get the best split service if you know how to choose your coverage wisely. Fortunately for you, we have gathered some helpful information here about choosing a new modem, a replacement modem, and additional tips.
What are the disadvantages?
The most significant disadvantage of having two separate broadband connections is being able to use them both at the same time, which can be very helpful when online shopping or streaming content.
Not only that, but you also have to remember which connection goes where! This becomes even more difficult if one connection has limited access due to it being connected to an area with poor signal strength.
It is also much harder to manage both connections all around the world depending on your needs and how busy each provider’s network is. For example, say you want to watch a movie and there is no clear Wi-Fi available, you will probably need to stop watching the film.
What should I choose?

Choosing between wireless broadband using a modem connected directly to your smartphone or computer, and having both ends connect via Wi-Fi is an excellent way to use internet.
With the first option you will need to find a compatible device that can be used as a modem and purchase this equipment separately. This can get expensive, especially if you are buying for a lot of people.
The second one costs less because you don’t have to buy separate pieces, but there is no guarantee that it will work properly outside of your home unless you invest in a good amount of WiFi technology.
Do I need both?

As mentioned earlier, having two separate modems is totally fine if you still want that high speed internet experience! Many people choose this option so they can have different levels of quality service depending on what area of the world they are in.
If you’re living somewhere with great cell phone reception but not very good wifi coverage, then using one modem connected to your smartphone and another modem plugged into your computer or gaming device is the way to go.
You get the best of both worlds by getting lower latency through the mobile connection, and fast broadband via the wired connection. This works beautifully for gamers who need solid performance while online as well as individuals who do most of their work and communication online.
What are the differences between wired and wireless modems?

Photo by Vladimir Srajber on Pexels
When choosing a modem for your computer, make sure it is able to connect using either a cable or wire-based connection (wired) with your computer or phone.
A wired connection uses cables that connect directly from one device to another. For example, you could use an Ethernet cord to connect your computer to your internet provider’s modem.
Wireless technology works similarly to how wifi functions today. A radio transmitter sends out small pulses that other devices can pick up and interpret as data.
What are the differences between routers and gateway devices?
A router is typically considered as being more powerful than a standard, non-smart device such as a modem or cable TV adapter. Routers have built-in networking features that allow you to connect multiple computers and other devices to share resources like Wi-Fi networks, broadband connections, and phone lines.
A gateway device does not offer advanced network functions, but it will make connecting to different services much easier. For example, most people do not need a complex software program to access Netflix, so most people just use a free browser add-on to do this. A gateway device with a good quality microphone can be used for voice calling too!
This article will talk about some of the best beginner level gateways available and how to use them. However, keep in mind that even though they are easy to use, these products are designed to work under hard conditions. They are meant to last through frequent usage, which means high data transfer speeds and strong signals are important.
Conclusion
Having two different internet providers in your home can seem confusing at times, but don’t worry! Here are all of the things you need to know about modem shopping for both personal and business use.
In this article, we covered everything from which frequencies each provider uses, to how much speed you get with each connection, to what types of modems are available. We also talked about why having multiple ISPs is a great way to find a deal online, and how to choose between them depending on your needs.
Now that you have the basics down, start looking around to see if there are any deals out there! And don’t forget to check our guide again for some helpful tips like choosing an account type that works for you, and always read through their terms and conditions before signing up.
Technology
The Case for Custom eLearning Platforms: Why Organizations Are Making the Switch

The corporate eLearning market has exploded in recent years, growing over 800% since 2000. As the demand for eLearning continues to accelerate, more and more organizations are finding that off-the-shelf solutions cannot keep pace with their training needs. This has led many companies to make the switch to custom-built eLearning platforms tailored specifically for their requirements.
There are several key reasons driving the demand for customized eLearning tools:
Greater Flexibility and Scalability
Generic eLearning software packages often impose rigid constraints that limit their ability to adapt to an organization’s evolving needs. Meanwhile, the “one-size-fits-all” approach fails to support the personalized learning critical for employee development. Custom platforms provide flexibility to add and modify features to match ever-changing business goals. As companies scale training across global workforces, custom solutions built on cloud infrastructure can scale seamlessly to handle growing demand.
Deeper Integration Across Systems
Smooth integration with existing HR, LMS, and other business systems is critical for optimizing training workflows. However, off-the-shelf tools rarely integrate well, creating data and process siloes. Custom platforms can tightly integrate role-based learning paths with core business applications, sync user profiles, enable single sign-on, and more. This level of integration catalyzes more impactful training function.
Better Data and Analytics
Generic software severely limits access to data insights that drive improvement. Custom platforms unlock a trove of analytics on content consumption, learner progression, platform adoption, and real-time feedback. Integrated analytics dashboards and APIs allow businesses to derive deep visibility across the learner lifecycle. These insights help continuously enhance learner experience, target development gaps, and demonstrate direct training ROI.
Enhanced Learner Engagement
For modern learners accustomed to consumer-grade digital experiences, poor platform usability quickly erodes engagement. Custom designs allow companies to incorporate familiar features from popular apps and websites while optimizing for their audience. Adaptive learning approaches further personalize content to individual styles and needs. With modular component architecture, custom platforms stay on the cutting edge of new modalities like AR/ VR to captivate learners.
Brand and Culture Alignment
Off-the-shelf tools impose a generic and often disruptive experience that clashes with existing brand identity and culture. In contrast, custom platforms allow organizations to carry over familiar styling, voice, and workflow patterns. Consistency in experience preserves brand recognition while smoother onboarding leads to wider adoption across all employee groups. Over time, the platform can evolve alongside cultural changes as well.
While custom elearning tools require greater upfront investment, for enterprise training needs, the long-term benefits far outweigh the costs. The ability to mold platforms to current and future needs results in greater leverage from learning spend.
As businesses demand ever-more from their learning technology, custom solutions provide the agility needed for true scale. Rather than forcing training functions into the constraints of generic software, custom elearning development keeps the focus on nurturing talent and capabilities. For any organization looking to drive workforce transformation through learning, custom elearning represents the way forward.
Technology
Pintarnya raises $16.7M to power jobs and financial services in Indonesia

Pintarnya, an Indonesian employment platform that goes beyond job matching by offering financial services along with full-time and side-gig opportunities, said it has raised a $16.7 million Series A round.
The funding was led by Square Peg with participation from existing investors Vertex Venture Southeast Asia & India and East Ventures.
Ghirish Pokardas, Nelly Nurmalasari, and Henry Hendrawan founded Pintarnya in 2022 to tackle two of the biggest challenges Indonesians face daily: earning enough and borrowing responsibly.
“Traditionally, mass workers in Indonesia find jobs offline through job fairs or word of mouth, with employers buried in paper applications and candidates rarely hearing back. For borrowing, their options are often limited to family/friend or predatory lenders with harsh collection practices,” Henry Hendrawan, co-founder of Pintarnya, told TechCrunch. “We digitize job matching with AI to make hiring faster and we provide workers with safer, healthier lending options — designed around what they can reasonably afford, rather than pushing them deeper into debt.”
Around 59% of Indonesia’s 150 million workforce is employed in the informal sector, highlighting the difficulties these workers encounter in accessing formal financial services because they lack verifiable income and official employment documentation.
Pintarnya tackles this challenge by partnering with asset-backed lenders to offer secured loans, using collateral such as gold, electronics, or vehicles, Hendrawan added.
Since its seed funding in 2022, the platform currently serves over 10 million job seeker users and 40,000 employers nationwide. Its revenue has increased almost fivefold year-over-year and expects to reach break-even by the end of the year, Hendrawn noted. Pintarnya primarily serves users aged 21 to 40, most of whom have a high school education or a diploma below university level. The startup aims to focus on this underserved segment, given the large population of blue-collar and informal workers in Indonesia.
Techcrunch event
San Francisco
|
October 27-29, 2025
“Through the journey of building employment services, we discovered that our users needed more than just jobs — they needed access to financial services that traditional banks couldn’t provide,” said Hendrawan. “We digitize job matching with AI to make hiring faster and we provide workers with safer, healthier lending options — designed around what they can reasonably afford, rather than pushing them deeper into debt.”

While Indonesia already has job platforms like JobStreet, Kalibrr, and Glints, these primarily cater to white-collar roles, which represent only a small portion of the workforce, according to Hendrawan. Pintarnya’s platform is designed specifically for blue-collar workers, offering tailored experiences such as quick-apply options for walk-in interviews, affordable e-learning on relevant skills, in-app opportunities for supplemental income, and seamless connections to financial services like loans.
The same trend is evident in Indonesia’s fintech sector, which similarly caters to white-collar or upper-middle-class consumers. Conventional credit scoring models for loans, which rely on steady monthly income and bank account activity, often leave blue-collar workers overlooked by existing fintech providers, Hendrawan explained.
When asked about which fintech services are most in demand, Hendrawan mentioned, “Given their employment status, lending is the most in-demand financial service for Pintarnya’s users today. We are planning to ‘graduate’ them to micro-savings and investments down the road through innovative products with our partners.”
The new funding will enable Pintarnya to strengthen its platform technology and broaden its financial service offerings through strategic partnerships. With most Indonesian workers employed in blue-collar and informal sectors, the co-founders see substantial growth opportunities in the local market. Leveraging their extensive experience in managing businesses across Southeast Asia, they are also open to exploring regional expansion when the timing is right.
“Our vision is for Pintarnya to be the everyday companion that empowers Indonesians to not only make ends meet today, but also plan, grow, and upgrade their lives tomorrow … In five years, we see Pintarnya as the go-to super app for Indonesia’s workers, not just for earning income, but as a trusted partner throughout their life journey,” Hendrawan said. “We want to be the first stop when someone is looking for work, a place that helps them upgrade their skills, and a reliable guide as they make financial decisions.”
Technology
OpenAI warns against SPVs and other ‘unauthorized’ investments
In a new blog post, OpenAI warns against “unauthorized opportunities to gain exposure to OpenAI through a variety of means,” including special purpose vehicles, known as SPVs.
“We urge you to be careful if you are contacted by a firm that purports to have access to OpenAI, including through the sale of an SPV interest with exposure to OpenAI equity,” the company writes. The blog post acknowledges that “not every offer of OpenAI equity […] is problematic” but says firms may be “attempting to circumvent our transfer restrictions.”
“If so, the sale will not be recognized and carry no economic value to you,” OpenAI says.
Investors have increasingly used SPVs (which pool money for one-off investments) as a way to buy into hot AI startups, prompting other VCs to criticize them as a vehicle for “tourist chumps.”
Business Insider reports that OpenAI isn’t the only major AI company looking to crack down on SPVs, with Anthropic reportedly telling Menlo Ventures it must use its own capital, not an SPV, to invest in an upcoming round.
-

 Trending3 weeks ago
Trending3 weeks agoCoinbase didn’t just lay off 14% of its staff due to AI. It replaced managers with ‘player-coaches’ and turned its org chart upside down
-

 Trending2 weeks ago
Trending2 weeks ago2026 MLB Trade Deadline Rumors Tracker: SF Giants Shopping High-Priced Core
-

 Trending2 weeks ago
Trending2 weeks agoThe Mandalorian and Grogu star Pedro Pascal says his Star Wars character “knows” Baby Yoda “will outlive him,” so he’s “making sure” Grogu “can survive in a world without him”
-
 News3 weeks ago
News3 weeks agoAstronomers Witness the Awesome Power of a Black Hole’s “Dancing Jets”
-
 Trending1 week ago
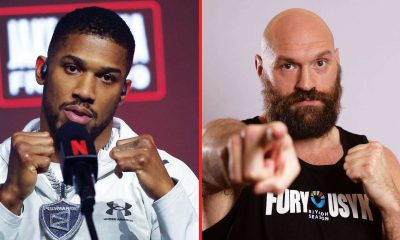
Trending1 week agoDerek Chisora makes new early KO prediction for Tyson Fury vs Anthony Joshua: “That’s his problem”
-

 Entertainment2 weeks ago
Entertainment2 weeks agoHeidi Klum worried Anna Wintour wouldn’t approve her Met Gala 2026 prosthetics
-

 Trending6 days ago
Trending6 days ago‘Lee Cronin’s The Mummy’ Comes to Digital, But When Will ‘The Mummy’ 2026 Be Streaming Free on HBO Max?
-

 News2 weeks ago
News2 weeks ago40,000 UC workers gird for a strike, disrupting medical services, cafeterias at all campuses